Today I was called by an allied sales from Oracle Switzerland (thanks Andreas). The main contact of the OCI tenant got an email in case of an identity service vulnerability in the past days. As I am not the main contact but the technical admin, I asked the tenant contact. An indeed, there was a mail arrived at 14th of June which was not forwarded to me.
Oracle Security Notification for Oracle Cloud Infrastructure (OCI) Identity Service vulnerability CVE-2022-21503 (Doc ID 2861245.1)
As a result of this vulnerability, administrators and their designees with read-access to the OCI audit-records in your tenancy could have viewed some credentials in clear text. These administrators and their designees could have used such credentials to authenticate as the associated principal.
You have the time to verify your account until July 18 2022 – otherwise it can cause outages.
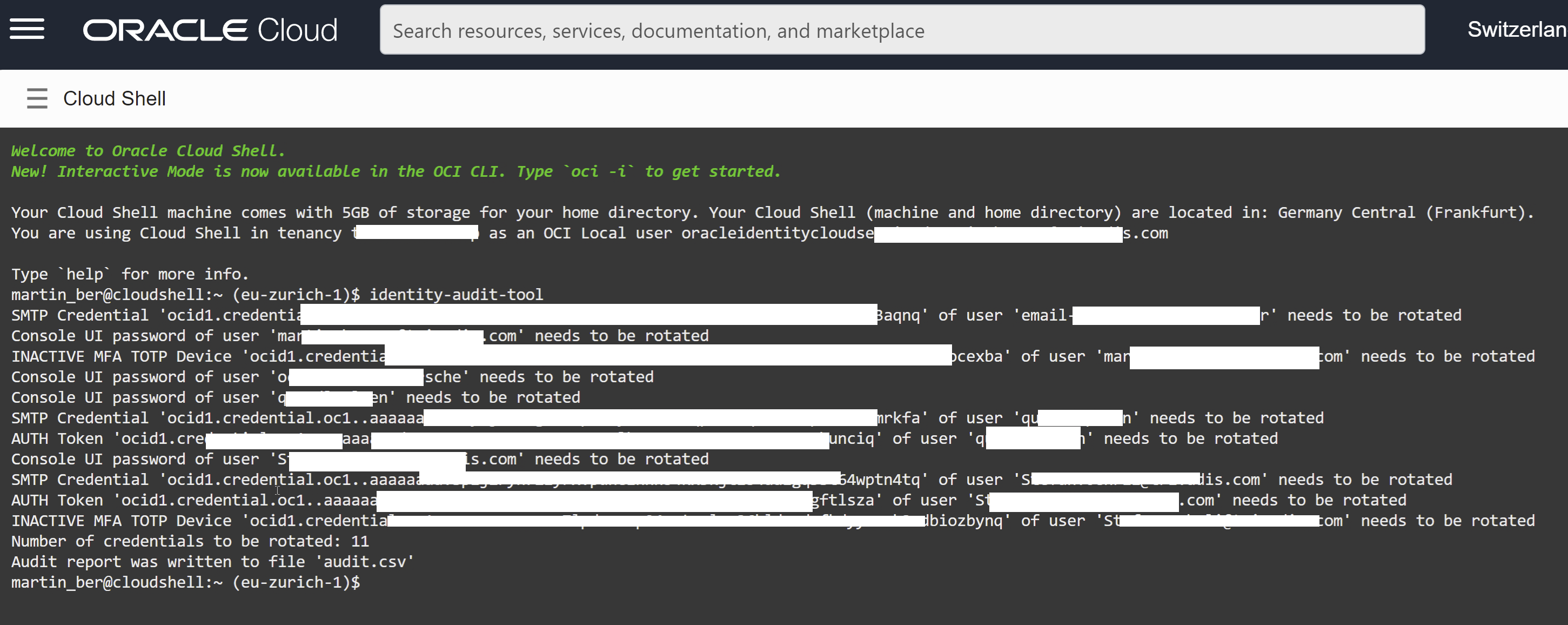
There is a tool called identity-audit-tool which can be executed in the cloud shell with administrator privileges to find out which accunts are affected – the solution for each type is described in the MOS note. Below this was the output in our development tenant – now I now what to do. The generated audit.csv file can be easily downloaded by the “hamburger menu”.
Update now your accounts and run the tool again. If the list has no results anymore – your job is done.