Cloud Security
When you search with the term “Cloud Breaches 2022” in one of the search engines, there is a almost endless list of breaches. In this 2-part blog post I show you an easy way, to level up your security in Oracle Cloud Infrastructure. For example listed on https://www.immuniweb.com/blog/top-10-cloud-security-incidents-in-2022.html:
- Flex Broker – It was found that the company was using an AWS S3 bucket to store data but failed to implement any security measures.
- BlueBleed Data Leak – 2.4 TB of Microsoft customer data belonging to more than 65,000 companies across over 100 countries was exposed due to a misconfigured Azure Blob Storage bucket.
- Pegasus Airlines – 6.5 TB of data, including sensitive flight data, source code, and personal information of flight crews due to a misconfigured AWS S3 bucket.
As you can see here, these are all issues related to security settings done by the owner of the accounts. No special hacking methods, no social engineering. Just wrong settings. Sure, there are also technical bugs possible, this one has happened in summer 2022 in Oracle Cloud Infrastructure and was called #AttachMe:
- Any unattached storage volume, or attached storage volumes allowing multi-attachment, could have been read from or written to as long as an attacker had its Oracle Cloud Identifier (OCID)
- Within 24 hours of being informed by Wiz, Oracle patched #AttachMe for all OCI customers. No customer action was required.
- Oracle declined to comment but thanked Gabay from Wiz.io in the firm’s July 2022 Critical Patch Update notes.
Cloud Security Risks – Items
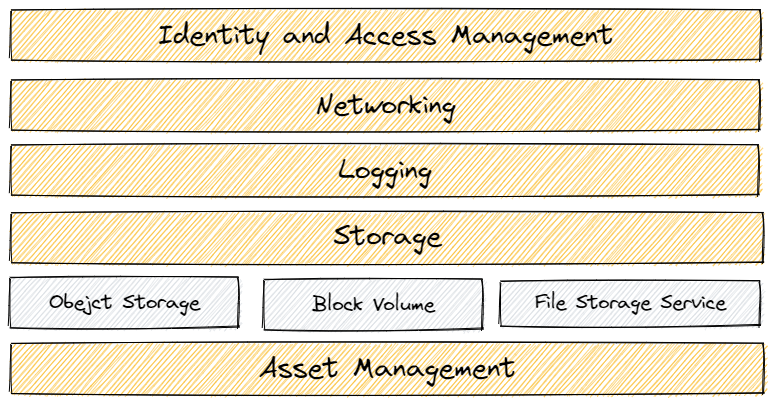
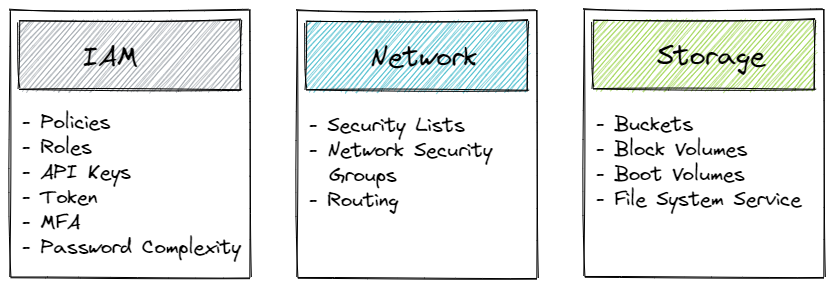
These items are all configurable by customer, like roles not according least-privilege principle, policies which allow the management of all cloud resources, MFA not enabled, non-complex passwords and so on. I grouped the OCI resources in three pillars. Each of them has to be considered to make your cloud account safe.
There are other risks like unpatched OS, old tools and many more. But this the next level, the focus here is all about the settings on level Oracle Cloud Infrastructure account.
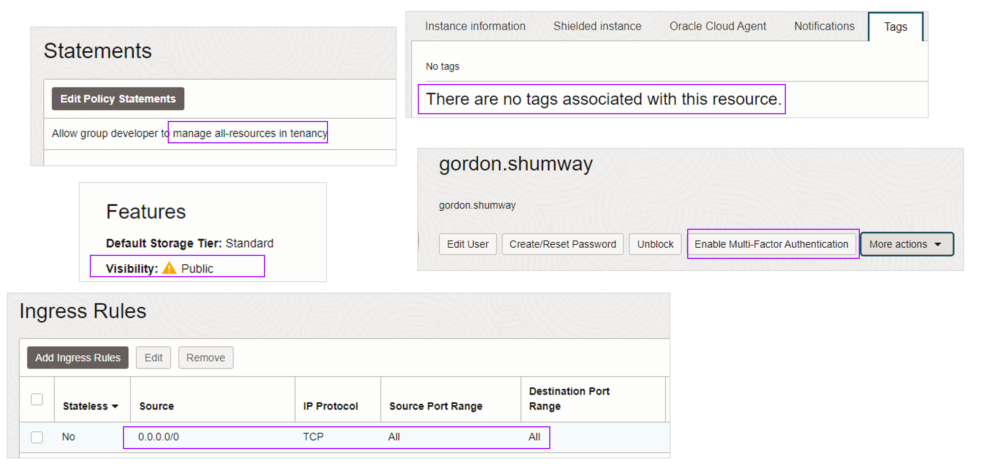
Some “best-of” Oracle Cloud Infrastructure settings – free risks included – found in a developer environment:
These issues are all highly dangerous, but they are easy to fix. The question is, how do I identify such configurations?
- First, read and understand the Oracle Cloud Infrastructure Security Checklist, which provides a lot of useful information about security in the cloud, shared security model, checklists and many more.
- Second, get support by CIS – Center of Internet Security.
CIS – Center of Internet Security
From the page https://www.cisecurity.org
- Etablished in 2000, a nonprofit organization that harnesses the power of a global IT community to safeguard public and – private organizations against cyber threats.
- The CIS Benchmarks are prescriptive configuration recommendations for more than 25+ vendor product families.
- Effort of cybersecurity experts globally to help you protect your systems against threats more confidently.
- Benchmarks, hardened images for cloud providers, training
- Cloud Providers, Desktop Software, OS, Mobile Devices etc.
- Free Access to Benchmarks
CIS offers security benchmarks for a whole bandwidth for topics like operating systems, cloud accounts, mobile phone operating systems, printers, cloud providers, and so on on a basic level for free. In Oracle Cloud Infrastructure, there is a CIS Hardended Oracle Linux 8 compute image available. After a short registration by mail, you can get all benchmarks for free. For Oracle Cloud Infrastructure, you can download the actual benchmark here: CIS Oracle Cloud Infrastructure Benchmarks (cisecurity.org). It is worth looking in from time to time for an updated version. The actual version is called CIS Oracle Cloud Infrastructure Foundations Benchmark v1.2.0 and covers this sections:
In the actual version 1.2.0, there are 48 recommendations how to make your cloud secure. I like this benchmark, because it’s not only about the settings, all issues are described, show the impact and how to eliminate it on console or OCI CLI.
Some recommendations:
- 1.1 Ensure service level admins are created to manage resources of particular service
- 1.8 Ensure user API keys rotate within 90 days or less
- 3.9 Ensure a notification is configured for VCN changes
- 3.17 Ensure write level Object Storage logging is enabled for all buckets
As I wrote above, it’s not so easy, and really not funny, to detect and solve such possible security breaches. And if you have done all of the CIS recommendations, there is always a change you get hacked. But most of the recommendations can be followed with a minimum effort, and each of these you made, your Oracle Cloud Infrastructure environment is more save.
Tool-Time
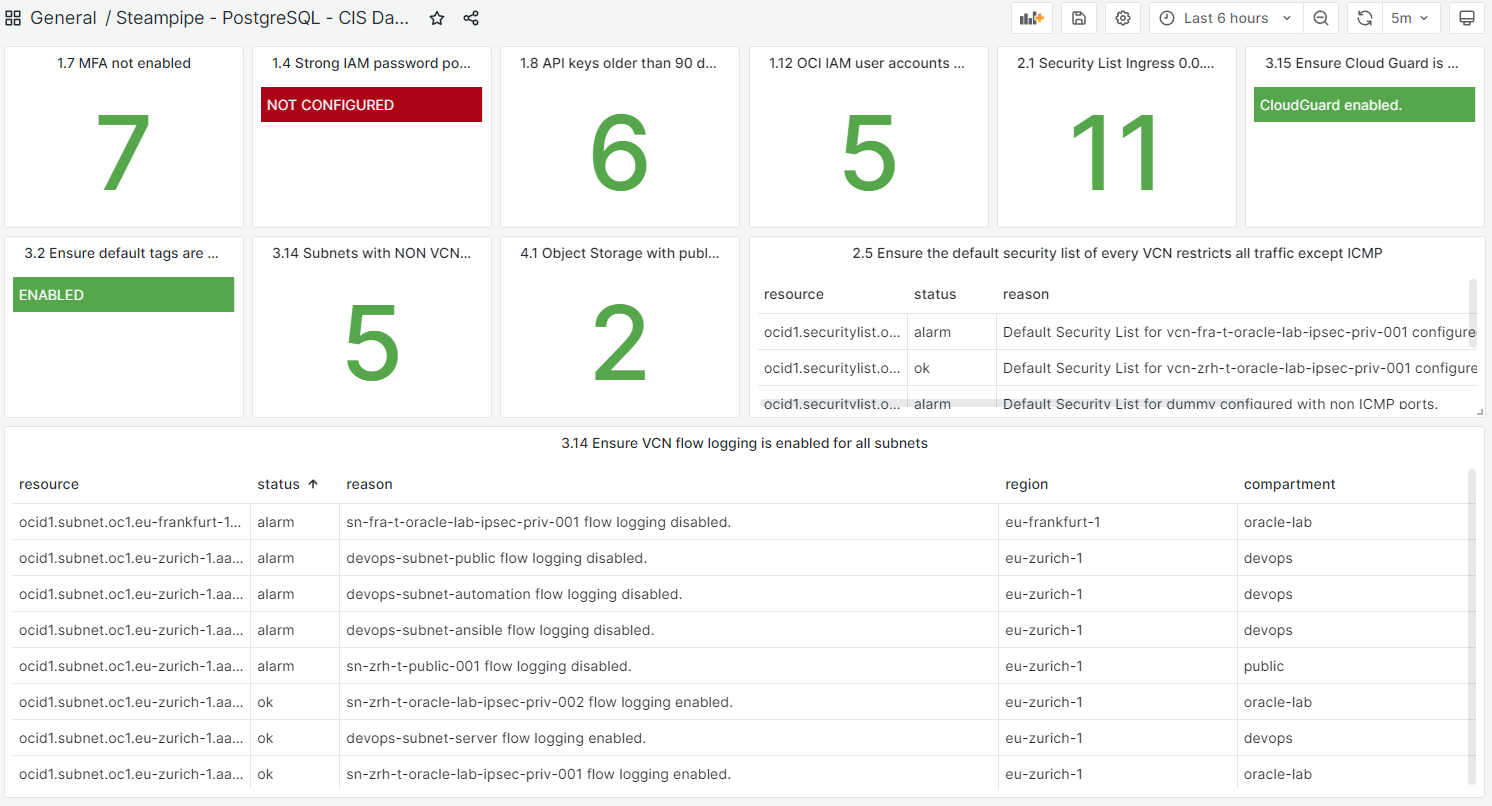
There are several tools on the market who check your security setting, like the commercial enterprise solution Prisma from Palo Alto. This tool gathers information like public object storage etc., based on CIS recommendations or self-defined metrics. A screenshot where you can see the vulnerabilities.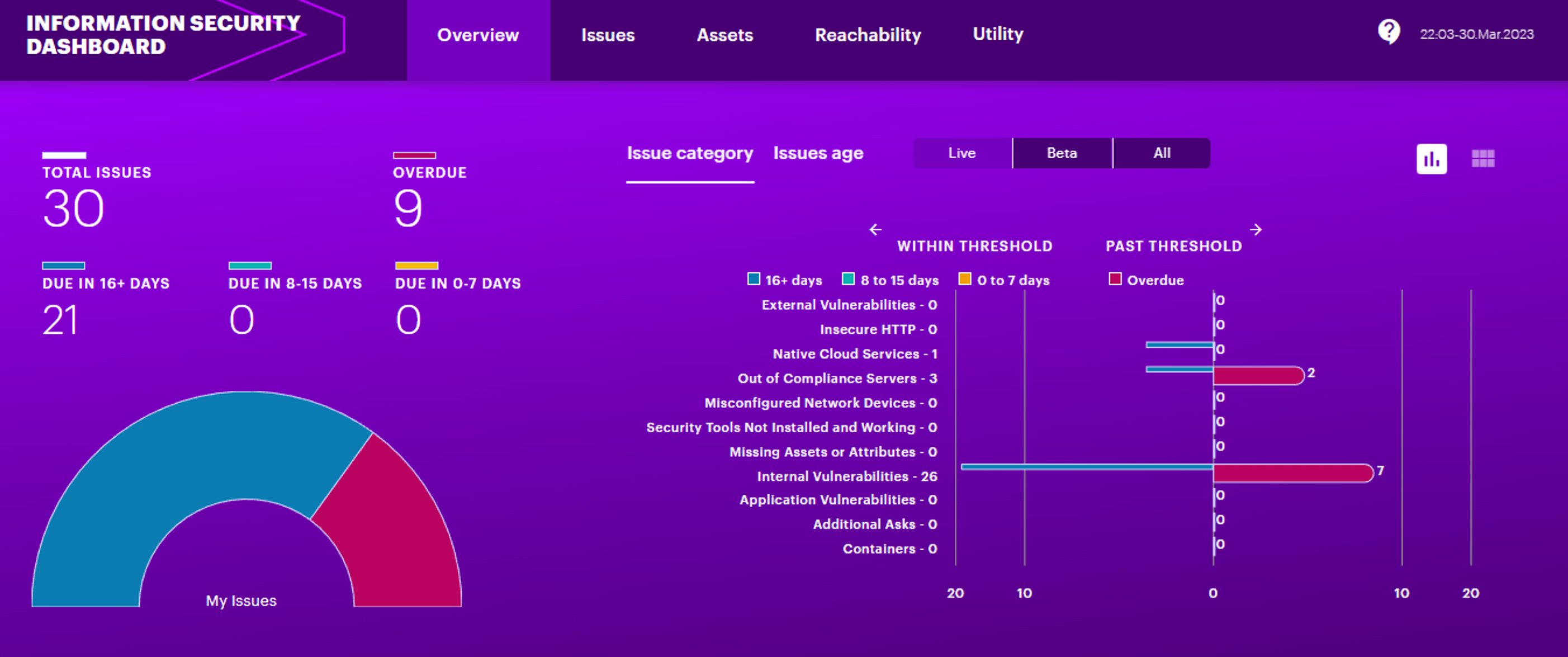
Oracle OCI has built-in checks in Cloud Guard too – see here: How to Monitor CIS Compliance with Oracle Cloud Guard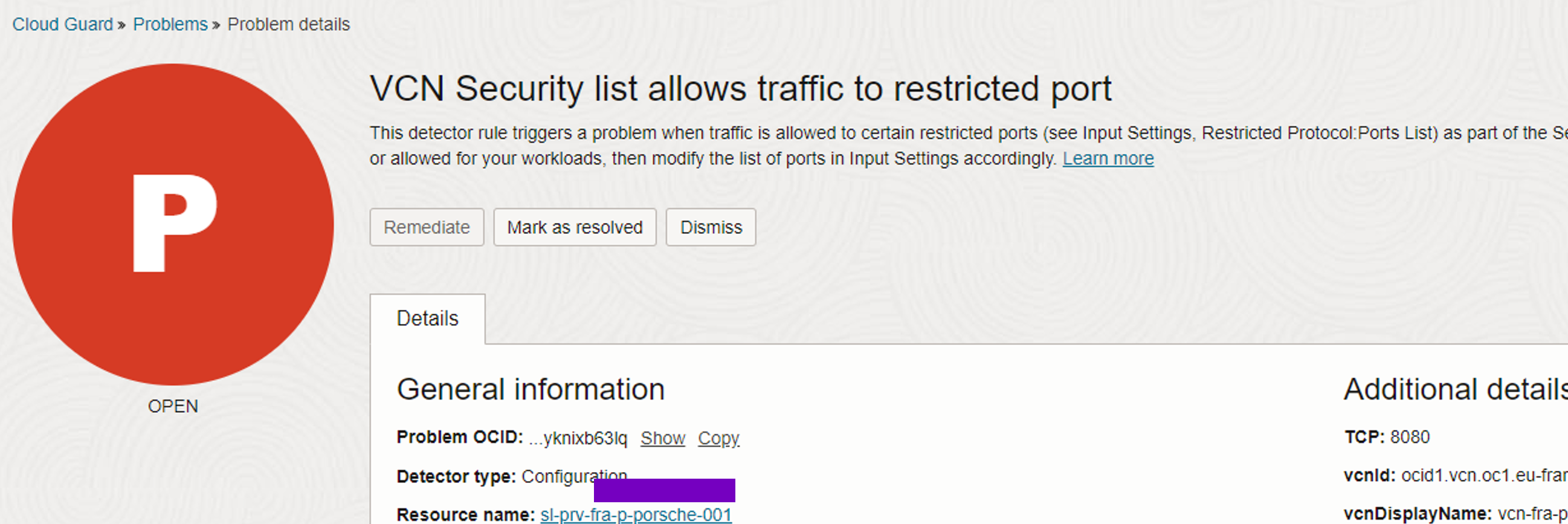
Summary Part 1
CIS is very helpful to bring security into your cloud account. The main questions are how do we identify these topics and how can we do a monitoring to recognize new issues. I showed you two well-know tools to get answers. The first tool is commercial, the second on is “on-demand” – but we want a free up-to-date dashboard to monitor live the current situation. And this is why we SELECT * FROM CLOUD; – a sneak peek below – follow part 2 next week.